Frequently Asked Questions About the Axios npm Supply Chain Attack by North Korea-Nexus Threat Actor UNC1069
A North Korea-nexus threat actor compromised the widely used axios npm package, delivering a cross-platform remote access trojan to potentially millions of developer environments during a three-hour window on March 31.
要点:
- The axios npm package, which has over 100 million weekly downloads, was compromised in a supply chain attack attributed by Google Threat Intelligence Group (GTIG) to UNC1069, a financially motivated North Korea-nexus threat actor.
- Malicious versions 1.14.1 and 0.30.4 were live on the npm registry for approximately three hours and delivered the WAVESHAPER.V2 backdoor to macOS, Windows and Linux systems.
- The malicious versions have been removed from npm, and developers who installed them are advised to treat affected systems as fully compromised, rotate all credentials and rebuild from clean snapshots.
背景
Tenable's Research Special Operations (RSO) team has compiled this blog to answer Frequently Asked Questions (FAQ) regarding a supply chain attack against the axios npm package.
常见问题
What happened to the axios npm package?
On March 31, 2026, an attacker published two malicious versions of the axios npm package, versions 1.14.1 and 0.30.4, to the npm registry. The attacker had compromised the maintainer account associated with the package and injected a malicious dependency called "plain-crypto-js" that served as a delivery vehicle for a cross-platform remote access trojan (RAT). The malicious versions were live on the npm registry for approximately three hours before they were identified and removed.
See how recent supply chain attacks are creating a black market for highly privileged developer credentials.
How popular is the axios npm package?
Axios is one of the most widely used JavaScript libraries, used to simplify HTTP requests. The 1.x branch typically has over 100 million weekly downloads, and the 0.x branch has over 83 million.
How was the axios maintainer account compromised?
According to analysis by StepSecurity and Google Threat Intelligence Group (GTIG), the attacker compromised the npm account belonging to @jasonsaayman and changed the associated email address to an attacker-controlled address ([email protected]).
The attacker used a long-lived classic npm access token to publish the malicious versions, bypassing the GitHub Actions OIDC workflow used for legitimate releases. Legitimate axios releases show a trusted publisher binding to GitHub Actions with a corresponding GitHub commit and tag. The malicious versions lacked this entirely, providing one of the clearest signals that the release was unauthorized.
What is the malicious dependency and how does it work?
The attacker published a purpose-built malicious package called [email protected] to npm approximately 22 minutes before publishing the first malicious axios version. A clean decoy version (4.2.0) was published roughly 18 hours earlier. The only change to the axios package itself was the addition of plain-crypto-js as a dependency in package.json. The package is never imported or referenced in axios source code.
When npm installs the compromised axios version, the plain-crypto-js package's postinstall hook executes an obfuscated JavaScript file called setup.js, which GTIG tracks as SILKBELL. This dropper uses a two-layer encoding scheme combining reversed Base64 and XOR cipher (key: "OrDeR_7077", constant: 333) to conceal its command-and-control (C2) URL and execution commands. It dynamically loads Node.js modules (fs, os, execSync) to evade static analysis.
After deploying the platform-specific payload, the dropper performs anti-forensic cleanup: it deletes itself, deletes the malicious package.json, and renames a clean stub file (package.md) to package.json, leaving a completely clean manifest upon post-infection inspection.
What malware does the attack deliver?
GTIG tracks the platform-specific payloads as WAVESHAPER.V2, an updated version of the WAVESHAPER backdoor previously attributed to UNC1069. WAVESHAPER.V2 variants exist for macOS (native C++ binary), Windows (PowerShell) and Linux (Python).
On macOS, the dropper downloads a Mach-O binary to /Library/Caches/com.apple.act.mond, disguised as an Apple system cache file.
On Windows, it copies the legitimate PowerShell executable to %PROGRAMDATA%\wt.exe (disguised as Windows Terminal) and uses a VBScript launcher to execute a downloaded PowerShell script with hidden execution and policy bypass flags. Windows persistence is achieved through a hidden batch file (%PROGRAMDATA%\system.bat) and a registry run key (HKCU:\Software\Microsoft\Windows\CurrentVersion\Run) named "MicrosoftUpdate."
On Linux, a Python RAT is downloaded to /tmp/ld.py and launched via nohup.
Regardless of platform, WAVESHAPER.V2 beacons to the C2 server every 60 seconds using Base64-encoded JSON and a hardcoded User-Agent string spoofing Internet Explorer 8 on Windows XP. The backdoor supports commands including:
- kill (terminate)
- rundir (filesystem enumeration)
- runscript (execute AppleScript)
- peinject (binary injection).
Who is behind this attack?
GTIG attributed this activity to UNC1069, a financially motivated North Korea-nexus threat actor active since at least 2018. The group has previously been tracked as both CryptoCore and MASAN by ClearSky (2020) and GTIG (2025), respectively. The attribution is based on the use of WAVESHAPER.V2 (a direct evolution of the WAVESHAPER backdoor previously attributed to UNC1069), infrastructure overlaps (connections from a specific AstrillVPN node previously used by UNC1069) and adjacent infrastructure on the same ASN historically linked to UNC1069 operations.
How quickly was the compromise detected?
Socket.dev's automated malware scanner detected the compromise within approximately six minutes of the first malicious version being published. Both malicious axios versions were removed from the npm registry approximately three hours after publication.
| Time (UTC) | Event |
|---|---|
| March 30, 05:57 | [email protected] (clean decoy) published |
| March 30, 23:59 | [email protected] (malicious) published with postinstall hook |
| March 31, 00:05 | Socket automated scanner detects compromise (~6 min) |
| March 31, 00:21 | [email protected] published |
| March 31, 01:00 | [email protected] published |
| March 31, 01:50 | Elastic Security Labs files GitHub Security Advisory to Axios repo |
| March 31, ~03:15 | npm unpublishes both malicious axios versions |
| March 31, 03:25 | npm initiates security hold on plain-crypto-js |
| March 31, 04:26 | Security stub replaces malicious package |
How widespread is the potential impact?
With over 100 million weekly downloads across both branches, the blast radius of a three-hour compromise window is significant. StepSecurity reported that its Harden-Runner tool detected anomalous C2 contact in over 12,000 projects. Hundreds of other npm packages depend on axios, amplifying the downstream exposure.
GTIG cautioned that "hundreds of thousands of stolen secrets could potentially be circulating" as a result of this and other recent supply chain attacks, potentially enabling further software supply chain compromises, SaaS environment breaches, ransomware events and cryptocurrency theft.
Are there indicators of compromise (IoCs)?
可以。GTIG published a comprehensive set of IoCs in their blog post as well as Socket.dev in addition to GTIG’s free GTI Collection for registered users. Types of IoCs available include network indicators (C2 domain and IPs), file hashes (SHA256 for all platform-specific payloads and the dropper), file system artifacts by platform, YARA rules for retrospective hunting and Google Security Operations detection rules.
Key network indicators to block: sfrclak[.]com and 142.11.206.73 (port 8000).
Is this related to other recent supply chain attacks?
This attack is one of several recent open-source supply chain compromises attributed to North Korea-nexus actors. GTIG noted that UNC6780 (also known as TeamPCP) recently poisoned GitHub Actions and PyPI packages associated with projects like Trivy, Checkmarx, and LiteLLM to deploy the SANDCLOCK credential stealer and facilitate follow-on extortion operations. While UNC1069 and UNC6780 are tracked as separate threat actors, the pattern of North Korea-nexus groups targeting open-source package ecosystems represents a broader trend.
What remediation steps are available?
The malicious axios versions (1.14.1 and 0.30.4) have been removed from the npm registry. Developers and organizations that installed either version are advised to:
- Downgrade to safe versions: [email protected] or [email protected]
- Remove the phantom dependency: node_modules/plain-crypto-js/
- Block C2 traffic to sfrclak[.]com and 142.11.206.73
- Treat affected systems as fully compromised: rotate all secrets and credentials, rebuild from clean snapshots
- Audit CI/CD pipelines: ephemeral runners require secret rotation; self-hosted runners are treated as fully compromised
- Search for file artifacts: /Library/Caches/com.apple.act.mond (macOS), %PROGRAMDATA%\wt.exe (Windows), /tmp/ld.py (Linux)
For long-term hardening, package managers now support version cooldown policies that prevent automatic installation of newly published versions:
| Package Manager | Setting |
|---|---|
| npm (v11.10.0+) | min-release-age=7d in .npmrc |
| pnpm (v10.16+) | minimum-release-age=7d |
| Yarn (v4.10+) | npmMinimalAgeGate: "7d" |
| Bun (v1.3+) | minimumReleaseAge = 604800 |
Has Tenable released any product coverage?
Yes, Tenable plugins that detect the compromised axios npm package and the malicious plain-crypto-js npm package are available.
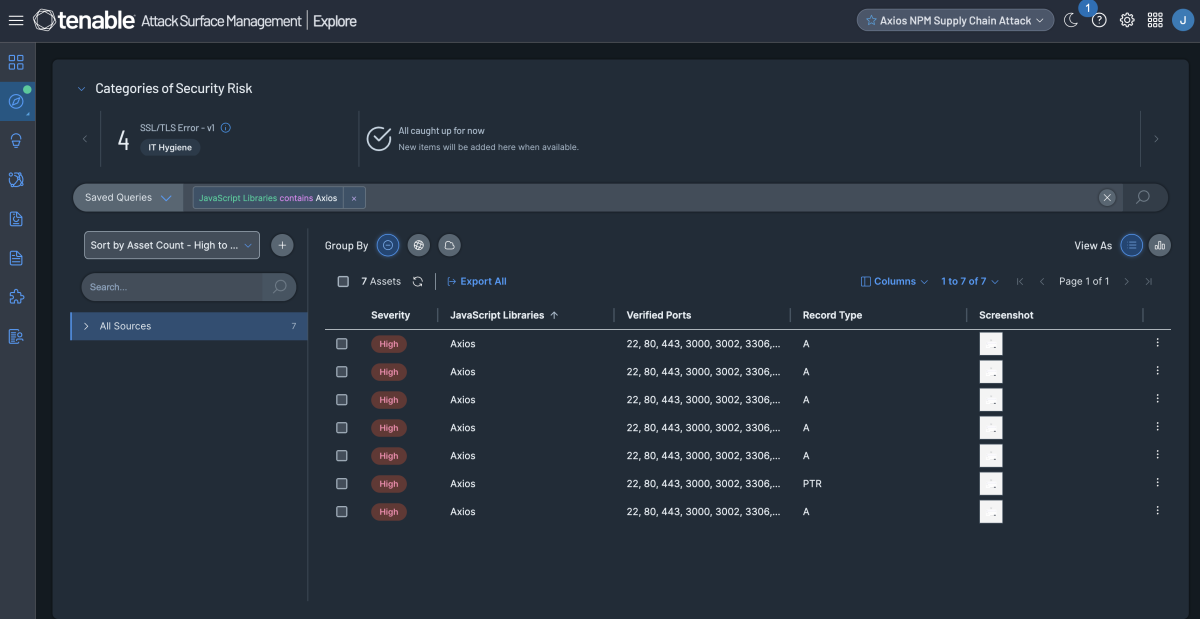
Additionally, customers can utilize Tenable Attack Surface Management to identify public facing assets running Axios libraries by utilizing the filter JavaScript Libraries contains Axios
获取更多信息
- GitHub Advisory: GHSA-fw8c-xr5c-95f9
- Google Threat Intelligence: North Korea-Nexus Threat Actor Compromises Widely Used Axios NPM Package in Supply Chain Attack
- Snyk: Axios npm Package Compromised in Supply Chain Attack
- Socket: Axios npm Package Compromised
- StepSecurity: Axios Compromised on npm
Join Tenable's Research Special Operations (RSO) Team on Tenable Connect and engage with us in the Threat Roundtable group for further discussions on the latest cyber threats.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
了解详情
- Exposure Management
- Vulnerability Management




Tenable One
申请演示
全球领先的由 AI 驱动的暴露风险安全管理平台。
谢谢
感谢关注 Tenable One。
我们的代表会尽快与您联系。
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success