
网络安全快照:AI Security Skills Drive Up Cyber Salaries, as Cyber Teams Grow Arsenal of AI Tools, Reports Find

网络安全快照:Cybersecurity Awareness Month Arrives To Find AI Security a Hot Mess, as New OT Security Guidelines Highlight Architecture Mapping
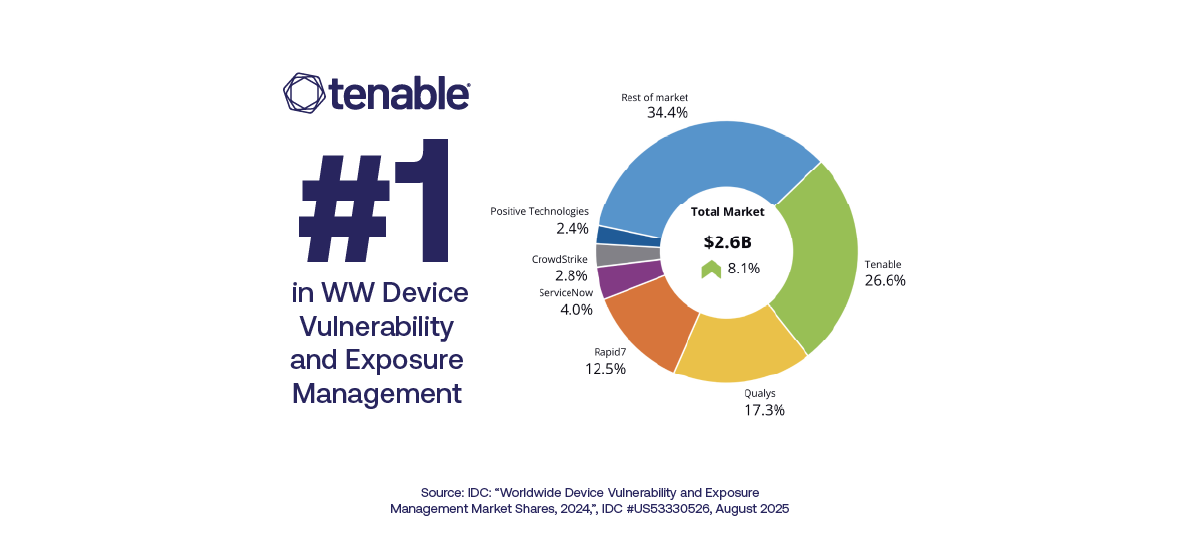
IDC 报告“Worldwide Device Vulnerability and Exposure Management Market Shares“将 Tenable 评为第一名








感谢您的订阅!
Form ID: 3971
Form Name: blog-subscribe
Form Class: c-form u-p--0 c-form--light c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: blog-subscribe-form-wrapper
Confirmation Class: blog-subscribe-confirmform-modal
Simulate Success