A benefit of an effective database security program is that organizations are better positioned to safeguard against the risks of compromise, and to thwart attacks such as malware and ransomware. Steps to building such a program include following best practices and regulatory requirements. Key initiatives include conducting and reviewing vulnerability assessments and compliance audits.
Databases typically contain sensitive material such as financial data, personnel information, business intelligence, client information, and more. Organizational secrets were once contained in a locked file cabinet, within secure rooms, or entombed deep within an organization. Access was controlled with a key requiring on-site access, and copying or removing files was difficult at best. Today, this information is commonly stored in a database that is connected to a wider network. Configuration errors can inadvertently provide access to a global audience. This practice makes a database a primary target of threat actors. Compromised databases are a common element of most data breaches, resulting in the exfiltration or loss of massive amounts of privileged information.
Information that is collected and stored in a database is important, and safeguarding that data is critical to business continuity. Costs associated with damages, fees, legal considerations and loss of reputation resulting from damaged and corrupt databases can be a financial burden for any organization. Depending on the type of data being stored, many established regulations and standards exist, which reduce the risk that information will be mishandled. Successful implementation means that customer confidence is maintained and organizations avoid costly financial ramifications.
Organizations are obligated to protect sensitive data and must frequently comply with laws and regulations regarding the data being stored. To best accomplish this, database teams require vulnerability details which easily identify the most significant vulnerabilities and provide guidance towards mitigation. The ability to act quickly in mitigating database vulnerabilities requires information to be presented in a manner which focuses on findings that should be prioritized and mitigated first. As a result, vulnerability remediation is more successful, the attack surface is reduced, and efforts can be visually tracked and measured against established goals.
Enumerating and securing your databases across the modern attack surface is especially critical related to 3-Tier Web Applications and AI. Nearly every Web Application has some flavor of database on the backend, and the internal and cybercriminal usage of GenAI and Agentic AI significantly raises the stakes for data security. GenAI prompts can be tied to your internal data, and AI agents can be granted a significant range of autonomy. AI agents can operate constantly, and adversaries can leverage low-and-slow attacks via these AI Agents and GenAI prompt-based crescendo attacks to gain access to your sensitive data. In this new world of AI, a strong database security program is not just about checking a box for compliance. It is a fundamental requirement to protect an organization's reputation and ensure AI remains an asset instead of a liability.
Tenable Security Center provides a risk-based view of your IT, security, and compliance posture, allowing database teams to analyze findings, remediate identified risk, track progress, and measure success. Designed with the principles of the Cyber Exposure Lifecycle in mind, this report assists database teams in maintaining a high level of awareness and vigilance. The report is tailored to guide the database team in detecting, predicting, and acting to reduce risk across their entire attack surface. The components provide a glance over detected Databases. From supported databases to unsupported databases, and exploitable databases that have been active for a long time, this report allows a database team to prioritize which assets/databases to patch first. The report also includes database compliance components that assist database teams by presenting pass/fail compliance results. It is important to note that the severity fields in the components can either be based on CVSS or VPR, depending on what the user selected in the settings. The report components do not require specific asset list filters to be applied prior to use. However, organizations that have teams that do focus on a specific group of assets will benefit from using custom asset lists. Database teams can visualize findings against database assets within the organization using this method.
Chapters
- Executive Summary: This chapter empowers the risk manager to quickly understand current database exposures across the network. Protecting sensitive information requires constant vigilance because adversaries leverage autonomous artificial intelligence agents to exploit hidden vulnerabilities. By transforming complex scanning data into accessible visual formats, the executive summary chapter allows the risk manager to understand the current impact of database vulnerabilities and misconfigurations. Furthermore, the provided insights guide the security operations team to effectively prioritize remediation efforts. Implementing a strong vulnerability management program ensures the organization protects critical data against unauthorized access while maintaining a resilient defense posture against evolving threats.
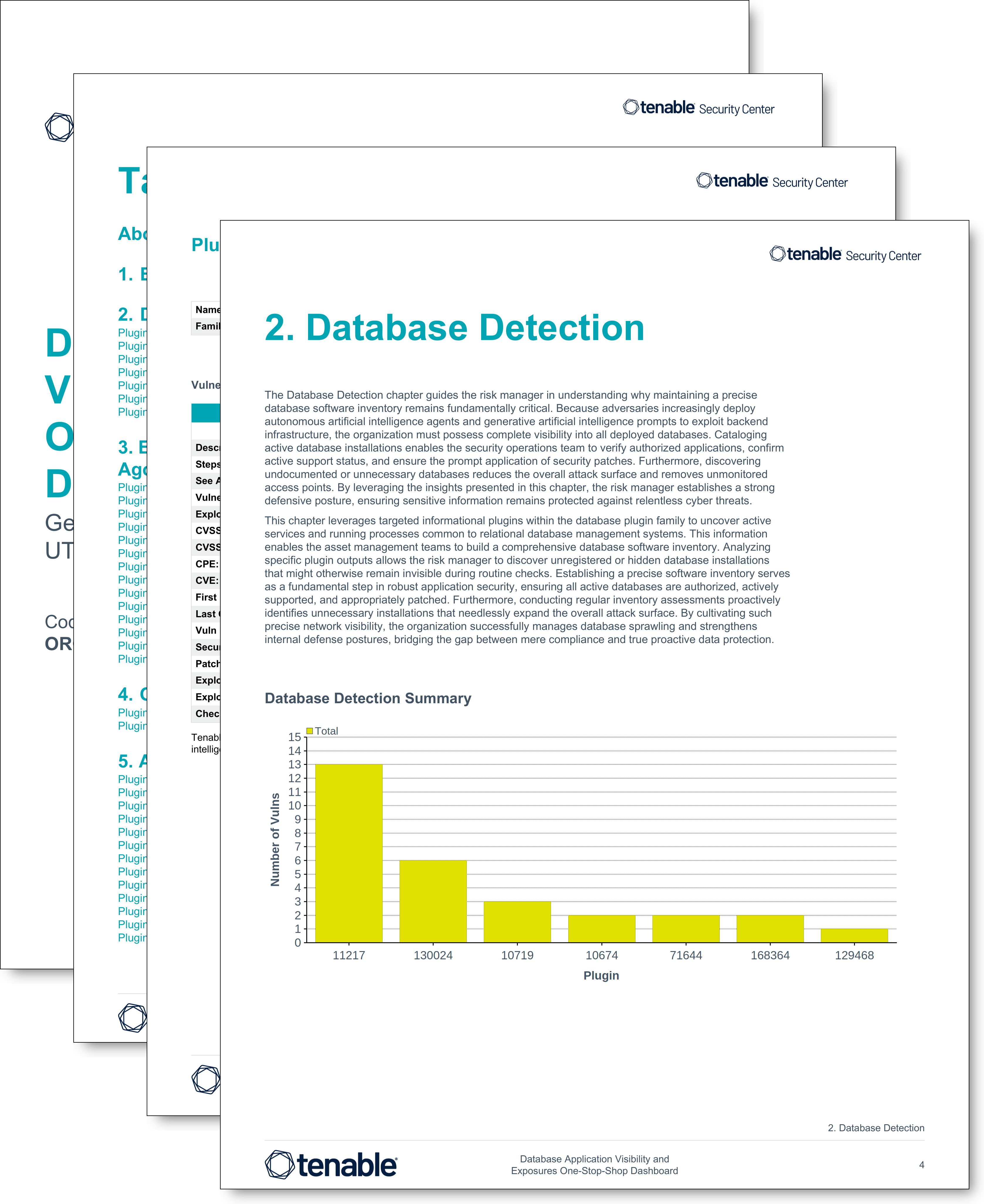
- Database Detection: This chapter guides the risk manager in understanding why maintaining a precise database software inventory remains fundamentally critical. Because adversaries increasingly deploy autonomous artificial intelligence agents and generative artificial intelligence prompts to exploit backend infrastructure, the organization must possess complete visibility into all deployed databases. Cataloging active database installations enables the security operations team to verify authorized applications, confirm active support status, and ensure the prompt application of security patches. Furthermore, discovering undocumented or unnecessary databases reduces the overall attack surface and removes unmonitored access points. By leveraging the insights presented in this chapter, the risk manager establishes a strong defensive posture, ensuring sensitive information remains protected against relentless cyber threats.
- Exploitable Database Vulnerabilities First Seen More Than 365 Days Ago: This chapter provides the risk manager a clear perspective regarding unresolved relational database vulnerabilities. When vulnerabilities remain active for over a year, the organization is exposed to substantial risk of unauthorized data access and system compromise. As the attack surface is prolonged, modern adversaries are able to take advantage of autonomous artificial intelligence agents and generative artificial intelligence prompts to exploit aging backend infrastructure. By identifying these neglected vulnerabilities, the risk manager is able to create a mitigation plan or strategy to close these exposure gaps across core database systems.
- Other Useful Database Findings: This chapter provides the risk manager a broader perspective regarding indirect vulnerabilities affecting relational database systems. Adversaries frequently exploit third-party applications and assets interacting with backend infrastructure. Because such supply chain exposures present a substantial risk of unauthorized data access, the organization must maintain complete visibility into the entire interconnected database ecosystem. By reviewing the structured findings within the chapter, the risk manager gains a comprehensive understanding of security gaps existing outside traditional database boundaries. Addressing the database-related vulnerabilities empowers the security operations team to strengthen internal defenses and protect sensitive information against relentless cyber threats.
- Audit Benchmarks Collected using Database Checks: This chapter empowers the compliance manager to comprehensively evaluate database configuration health against established compliance standards. Because databases secure sensitive organizational data, proper configuration remains essential to prevent unauthorized access and data breaches. Compliance authorities prescribe stringent frameworks, such as 800-53 and PCI-DSS, to guide secure configurations. To maximize effectiveness, the organization must establish a customized best practice configuration policy guide and modify scanning audit files to strictly enforce approved internal standards. When interpreting the findings within the chapter, the compliance manager must understand that severity levels carry specific meanings for audit results. A high severity finding indicates a failed audit check, an informational severity signifies a successfully passed check, and a medium severity dictates a manual review is required. Grasping these distinct severity definitions empowers the system administrators to accurately measure compliance and strengthen overall network defenses.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success