The risk manager and security operations team need full visibility of all vulnerabilities within the organization. By leveraging the continuous asset scanning and automated risk prioritization capabilities of Tenable Security Center (formerly Tenable.sc), the security operations team is able to discover operating system and application instances, software vulnerabilities, misconfigurations and other exposure details. This report provides a high-level summary of asset counts per operating system and discovered applications, with the added benefit of helpful queries to identify troublesome areas in scan fidelity.
A key first step in establishing an exposure management program is to separate findings by operating systems and applications. This discovery process helps to assess the technology in the environment and discover gaps in exposure management. The components in the report focus on either operating system vulnerabilities or application vulnerabilities by leveraging the CPE (Common Platform Enumeration) strings that are defined by NIST (National Institute of Standards and Technology) and provide a unique, standardized name for IT products. Using this comprehensive approach to data analysis, the risk manager is able to obtain visibility into the network and prioritize mitigation efforts accordingly.
Once the vulnerabilities are known to the risk managers, the risk prioritization begins. In cases where a vendor-supplied patch is available, patch management solutions are able to increase efficiency by distributing and applying the patches. However, there are many cases where unsupported operating systems or patches have not been released yet. Oftentimes unpatchable vulnerabilities are identified as exploitable, and to remediate the risk requires a configuration change such as a registry key change, disabling insecure or deprecated protocols, and upgrading to a supported operating system version or new operating system.
As the exposure management program matures, the security operations team needs to begin to measure data collection and the remediation processes. To allow for accurate measurements, the fidelity of the scanning program needs to be reviewed and monitored. To assist in this process, the report has several chapters that enable the understanding of scan health by identifying gaps in the scan activities. Organizations that utilize both agent scans and network scans are able to benefit from each method and begin to close the gaps in scan coverage. The report helps to show the health of credentialed network scans, also known as an authenticated scan (which provides a deeper insight into the risk posture of the asset), as compared to discovery scanning. If credentialed network scans are not available, the organization can leverage the Tenable Agent to collect vulnerability data. While agents are not designed to perform network checks, certain settings cannot be checked or obtained, therefore combining network scans with agent-based scanning eliminates this gap. The key thing to keep in mind is that scanning with credentials will provide the most complete asset info, vulnerability and patch auditing picture with a regular scanning cadence and depth. Local Check Scans with the Tenable Agent or working credentials will provide the more complete and hi-fidelity data set to ensure the good data passes downstream for reporting, workflows and stakeholders.
Tenable Security Center provides the ability to know the vulnerabilities on the network and provides full visibility with continuous asset scanning and automated risk prioritization capabilities. The data on this report helps to expose gaps and facilitate the process in which the risk manager is able to quickly find highly exploitable, business-impacting vulnerabilities using risk-based threat intelligence and critical asset identification. As the risk mitigation efforts increase their effectiveness, the CISO is able to close the critical exposures and make rapid, decisive decisions that direct actions to mitigate high-risk vulnerabilities and communicate to leadership and stakeholders the current state of the exposure management program.
Chapters
- Executive Summary: This chapter provides the risk manager with a high-level overview of scan health and vulnerability metrics across the organization. By analyzing charts and tables the risk manager and the security operations team are able to observe at a high level the status of routine scanning and risk mitigation activities. The components help to categorize unresolved flaws within software and infrastructure based on severity, exploitability, and patch availability to pinpoint areas requiring immediate remediation.
- Tenable Agent Findings: This chapter provides details related to Tenable Agents. Details include informational data, such as the detection of Tenable Agent installations, as well as Tenable Agent vulnerability data, such as out-of-date or software end-of-life (SEoL) Tenable Agents, including potential third-party induced vulnerabilities to Tenable Agents from other products.
- Asset Inventory: This chapter provides summary counts for operating systems and applications detected within a network over a thirty-day period. The tables utilize Nessus and Tenable Agent to identify active platforms, including an extensive list of installed software and libraries.
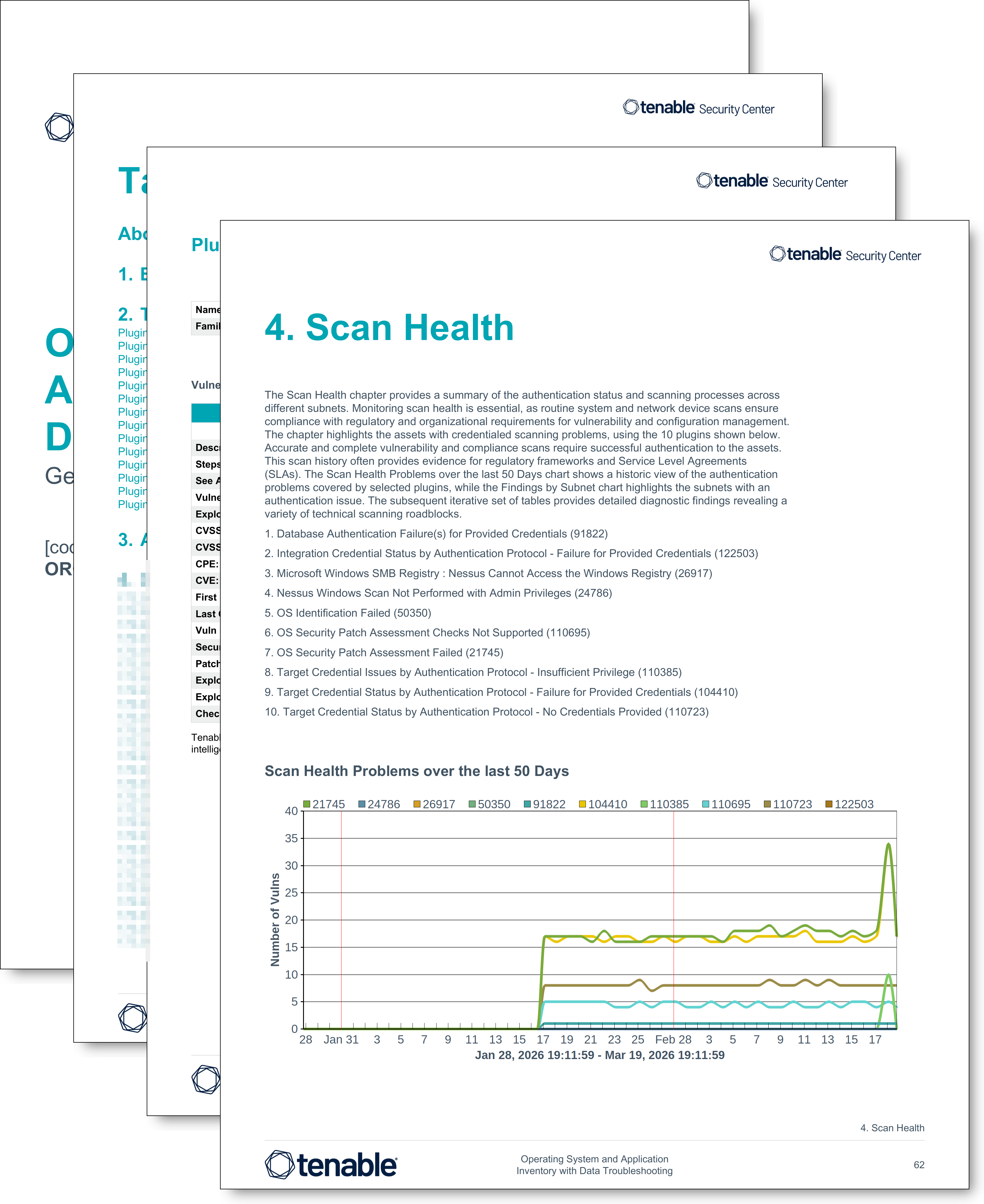
- Scan Health: This chapter provides a summary of the authentication status and scanning processes across different subnets. Monitoring scan health is essential, as routine system and network device scans ensure compliance with regulatory and organizational requirements for vulnerability and configuration management. The chapter highlights the assets with credentialed scanning problems.
- Operating System Exposure: This chapter filters for operating system vulnerabilities last seen within the past 30 days, categorizing the vulnerabilities across critical, high, medium, and low severity levels. While the resulting data reveals unresolved flaws across the network, a risk manager uses the information to establish a valuable baseline.
- Exploitable Operating System Exposure: This chapter filters for exploitable operating system vulnerabilities last seen within the past 30 days, categorizing the findings across critical, high, medium, and low severity levels. While the resulting data reveals unresolved flaws across the network, the information establishes a valuable baseline and highlights an exploitable vulnerability backlog.
- Security End of Life (SEoL) Operating Systems: The data in this chapter reveals unresolved flaws across various unsupported platforms and provides the operations team with a list of risk mitigation steps. Operating systems that have reached their end-of-life date are a major cause of data breaches as vendors stop offering support, which causes security and stability to decrease over time. Risk managers performing analysis of end-of-life systems are able to guide the security operations team away from a reactive state and into a prioritized, proactive posture hunting for actively unsupported operating systems.
- Unpatchable and Exploitable Operating Systems: This chapter serves as a critical diagnostic tool, guiding the risk manager to identify severe exposures across the organization. The chapter specifically filters for operating system vulnerabilities detected over the past thirty days lacking a published patch but possessing known exploits. By highlighting assets suffering from unpatchable flaws, the data reveals problems the organization cannot currently solve through traditional patching.
- Application Exposure: This chapter functions as a foundational resource guiding the risk manager to uncover software vulnerabilities across the network. The risk manager uses the data in this chapter to establish a comprehensive view of the attack surface and pinpoint severe exposures challenging the organization.
- Exploitable Application Exposure: This chapter empowers the risk manager to uncover critical software vulnerabilities across the network. By leveraging authenticated scans, the chapter filters for findings using the Application CPE string 'cpe:/a' last observed within the past thirty days, categorizing unresolved application flaws with an available exploit across critical, high, medium, and low severity levels. The risk manager uses the resulting data to establish a comprehensive view of the attack surface and pinpoint severe exposures challenging the organization
- Security End of Life Applications: This chapter enables the risk manager to effectively identify unsupported software across the organization. When applications reach an end-of-life status, software vendors permanently cease offering support and halt all releases of new security patches. Consequently, operating unsupported software causes security and network stability to continually degrade over time, leaving the organization increasingly vulnerable to cyber attacks. By identifying unsupported applications, the risk manager guides the security operations team to mitigate risks that surface from the severe dangers of utilizing outdated products.
- Unpatchable Exploitable Application Exposure: This chapter equips the risk manager to proactively identify highly dangerous software vulnerabilities across the organization. Recognizing unpatchable and actively exploitable software presents an essential mentoring opportunity. When researchers publish a new vulnerability, a delay often occurs before the vendor develops and releases an official patch. Malicious actors highly value the unprotected time gap, utilizing readily available exploit frameworks to launch targeted attacks against the organization before a permanent fix exists.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success