CVE-2025-25256: Proof of Concept Released for Critical Fortinet FortiSIEM Command Injection Vulnerability
Exploit code is reportedly available for a critical command injection vulnerability affecting Fortinet FortiSIEM devices.
Background
On August 12, Fortinet published a security advisory (FG-IR-25-152) for CVE-2025-25256, a critical command injection vulnerability affecting Fortinet FortiSIEM.
| CVE | Description | CVSSv3 |
|---|---|---|
| CVE-2025-25256 | Fortinet FortiSIEM Command Injection Vulnerability | 9.8 |
Analysis
CVE-2025-25256 is a critical operating system (OS) command injection vulnerability affecting Fortinet FortiSIEM. A remote, unauthenticated attacker can exploit this flaw to execute arbitrary code using specially crafted requests.
According to the advisory, exploitation of this flaw does not “produce distinctive” indicators of compromise (IoCs). As such, it may be difficult to identify that a device has been compromised.
Historical Exploitation of Fortinet Devices
Fortinet vulnerabilities have historically been common targets for cyber attackers, with 20 CVEs currently on the Cybersecurity and Infrastructure Security Agency’s (CISA) Known Exploited Vulnerabilities (KEV) list. The following table outlines some of the most impactful Fortinet vulnerabilities in recent years.
Proof of concept
At the time the advisory was published by Fortinet on August 12, they warned that “practical exploit code” had been found in the wild, though they did not provide a link to the exploit. Tenable Research has attempted to identify a functional proof-of-concept (PoC) for this flaw, however, we have not successfully located one as of the time this blog was published.
Solution
The following table details the affected and fixed versions of Fortinet devices for CVE-2025-25256:
| Product Version | Affected Range | Fixed Version |
|---|---|---|
| FortiSIEM 5.4 | All Versions of 5.4 | Migrate to a fixed release |
| FortiSIEM 6.1 | All Versions of 6.1 | Migrate to a fixed release |
| FortiSIEM 6.2 | All Versions of 6.2 | Migrate to a fixed release |
| FortiSIEM 6.3 | All Versions of 6.3 | Migrate to a fixed release |
| FortiSIEM 6.4 | All Versions of 6.4 | Migrate to a fixed release |
| FortiSIEM 6.5 | All Versions of 6.5 | Migrate to a fixed release |
| FortiSIEM 6.6 | All Versions of 6.6 | Migrate to a fixed release |
| FortiSIEM 6.7 | 6.7.0 through 6.7.9 | 6.7.10 or above |
| FortiSIEM 7.0 | 7.0.0 through 7.0.3 | 7.0.4 or above |
| FortiSIEM 7.1 | 7.1.0 through 7.1.7 | 7.1.8 or above |
| FortiSIEM 7.2 | 7.2.0 through 7.2.5 | 7.2.6 or above |
| FortiSIEM 7.3 | 7.3.0 through 7.3.1 | 7.3.2 or above |
| FortiSIEM 7.4 | Not Affected | Not Applicable |
Fortinet’s security advisory advises if immediate patching is not able to be performed, they recommend limiting access to the phMonitor port of 7900. We strongly recommend reviewing the advisory for updates as well as the latest on mitigation or indicators of compromise (IoCs).
Identifying affected systems
A list of Tenable plugins for this vulnerability can be found on the individual CVE page for CVE-2025-25256 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline.
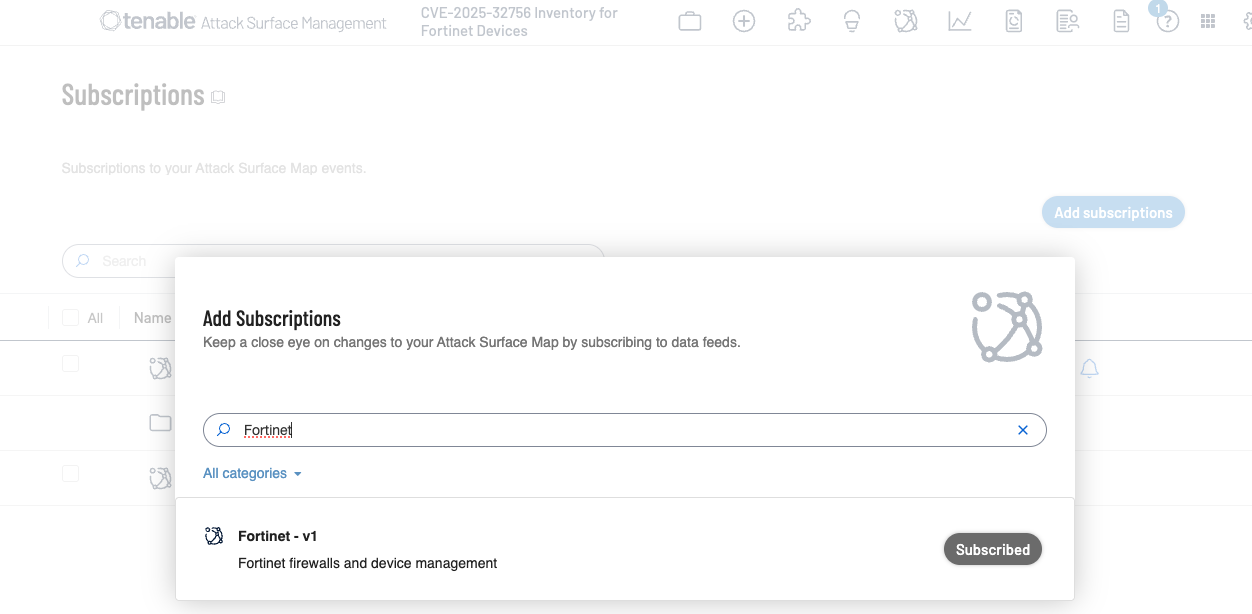
Additionally, customers can utilize Tenable Attack Surface Management to identify public facing assets running Fortinet devices by using the following subscription:
Get more information
Join Tenable's Research Special Operations (RSO) Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
Learn more
- Exposure Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success