Synopsis
A stored cross-site scripting vulnerability exists in the Web UI. A remote, authenticated attacker is able to inject malicious client-side code into the 'URL/ Host / Connection' form in the 'DATA TO SERVER' configuration section. An attacker with low privileges could exploit this to steal session details from a higher privileged user.
Proof of Concept
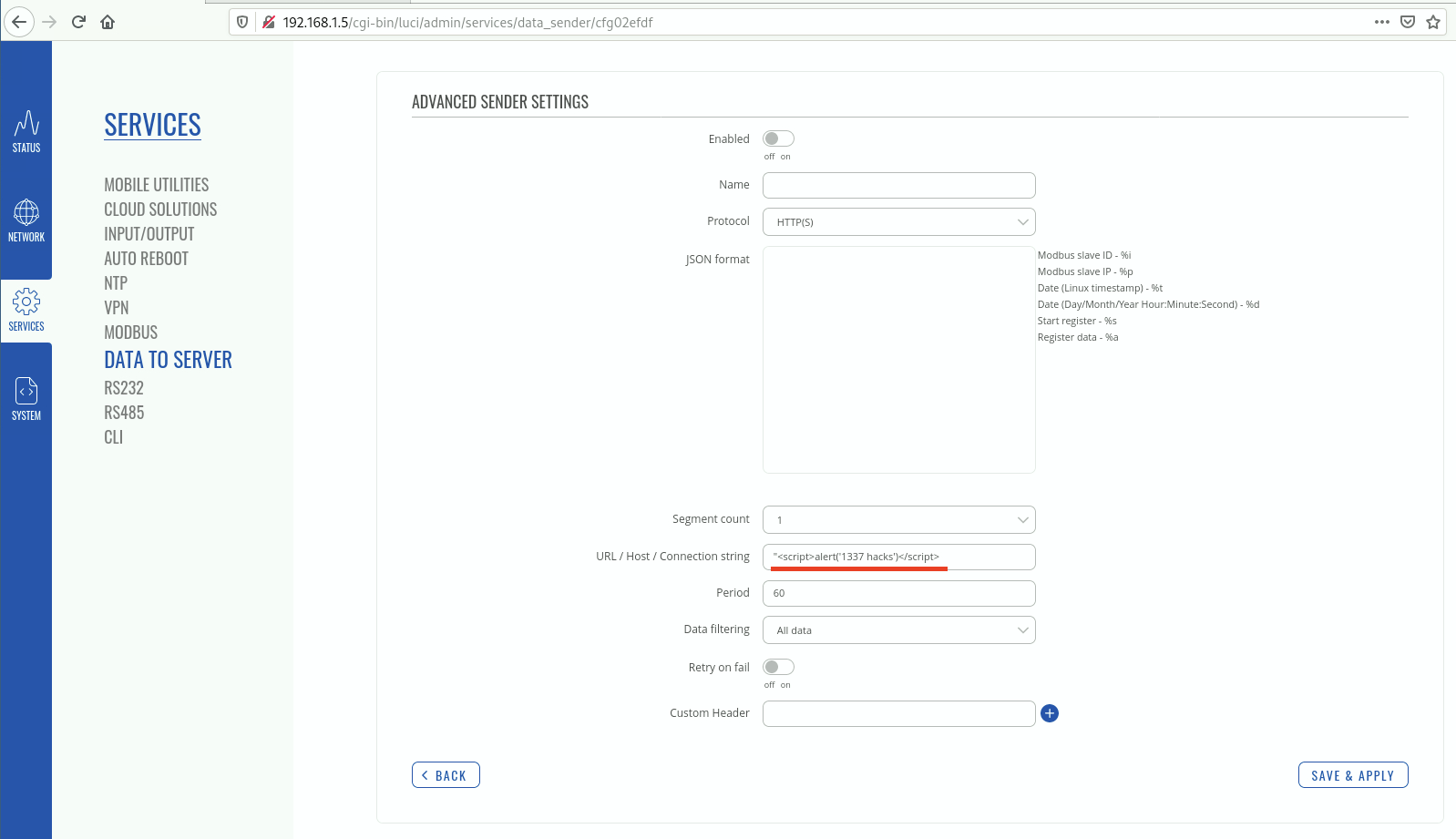
In the below screenshot we can see the tester has added some script tags into the 'URL/ Host / Connection' form.
“<script>alert(‘1337 hacks’)</script>
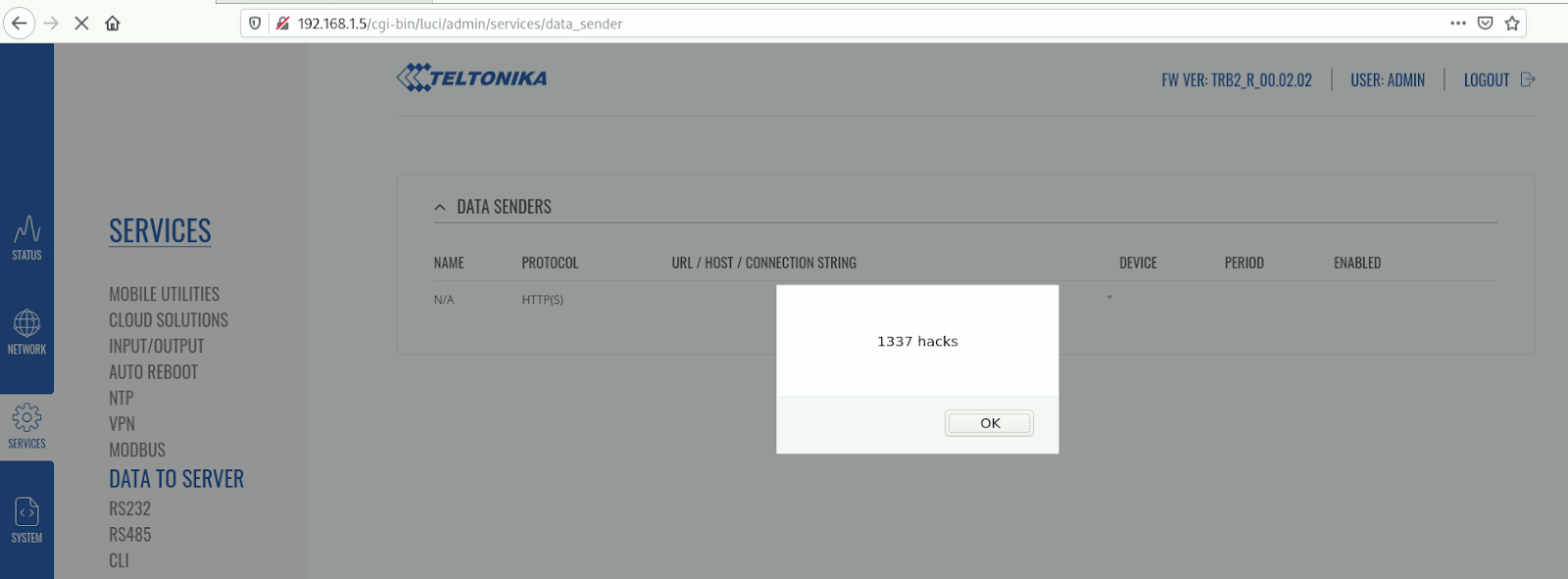
When the tester selects ‘Save & Apply’ this change you will be redirected to the list of data sensors and the injected javascript will execute.
Solution
Upgrade to TRB2_R_00.02.03 or newer.Additional References
https://wiki.teltonika-networks.com/view/TRB245_Firmware_Downloads#TRB2XX_R_00.02.03.1_.7C_2020.05.15Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success